The most relevant questions about ransomware and the No More Ransom project.
- 1989: The first known ransomware, the 1989 AIDS Trojan (also known as «PC Cyborg»), is written by Joseph Popp
- 2005: In May, extortion ransomware appears
- 2006: By mid-2006, worms such as Gpcode, TROJ.RANSOM.A, Archiveus, Krotten, Cryzip, and MayArchive start using more sophisticated RSA encryption schemes, with ever-increasing key-sizes
- 2011: A ransomware worm imitating the Windows Product Activation notice appears
- 2013: A ransomware worm based on the Stamp.EK exploit kit surfaces and a Mac OS X-specific ransomware worm arrives on the scene. CryptoLocker rakes in around $5 million in the last four months of the year
- 2015: Multiple variants on multiple platforms are causing major damage
Encryption Ransomware
- It encrypts personal files and folders (documents, spread sheets, pictures, and videos).
- The affected files are deleted once they have been encrypted, and users generally encounter a text file with instructions for payment in the same folder as the now-inaccessible files.
- You may discover the problem only when you attempt to open one of these files.
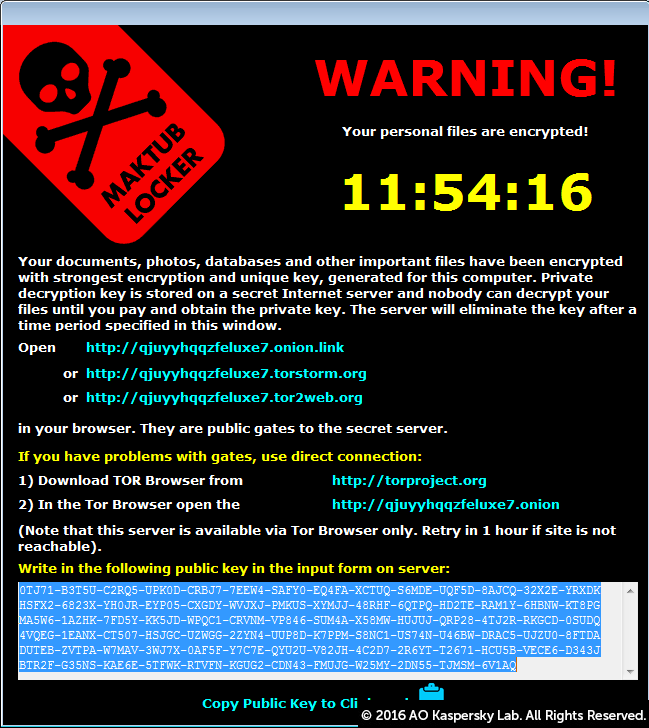
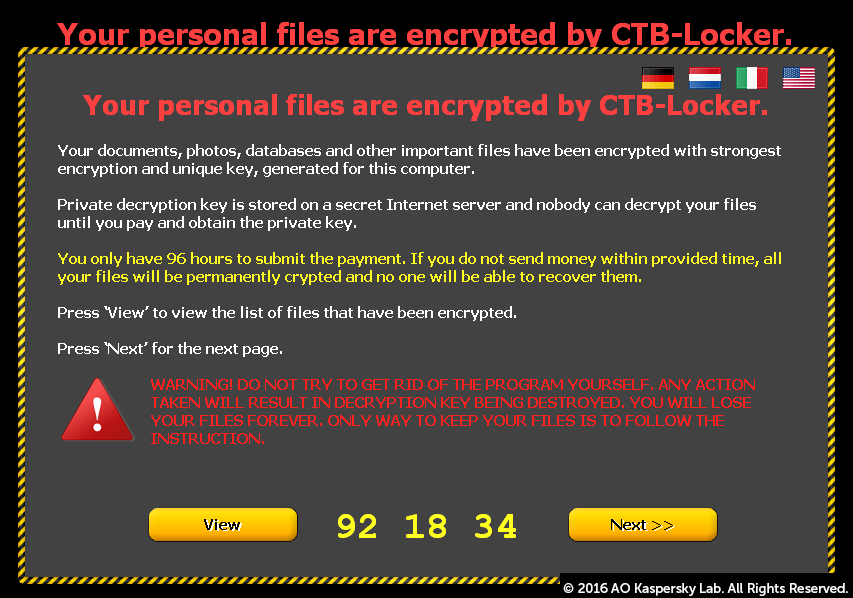
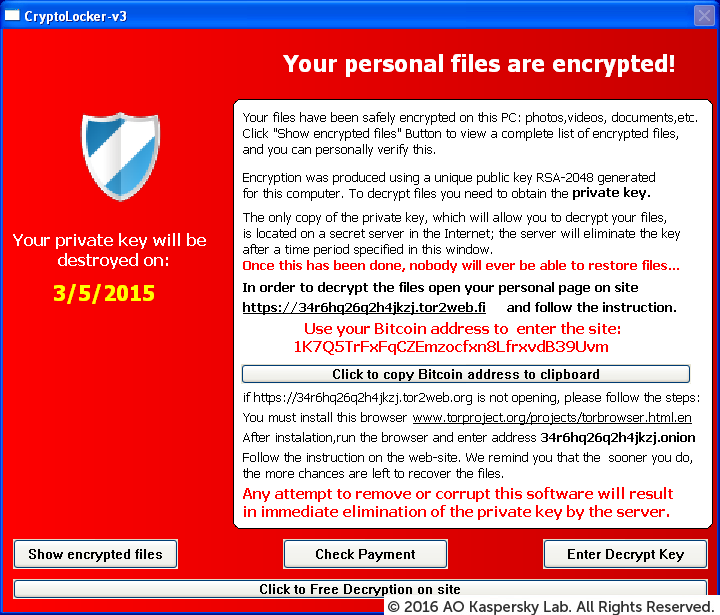
- Some, but not all types of encryption software show a ‘lock screen’:
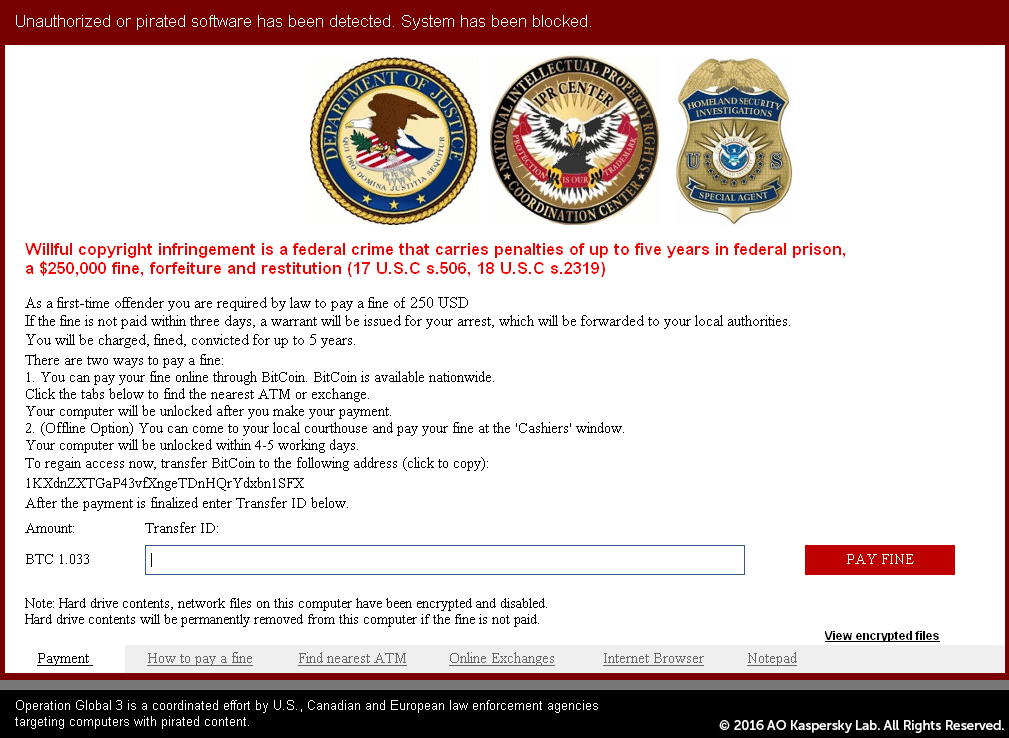
Lock Screen Ransomware — WinLocker
- It locks the computer’s screen and demands payment.
- It presents a full screen image that blocks all other windows.
- No personal files are encrypted.
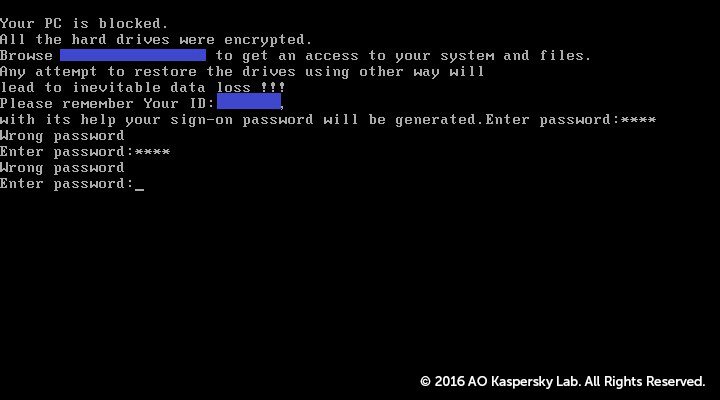
Master Boot Record (MBR) Ransomware
- The Master Boot Record (MBR) is the part of the computer’s hard drive that allows the operating system to boot up.
- MBR ransomware changes the computer’s MBR so that the normal boot process is interrupted.
- Instead, a ransom demand is displayed on the screen.
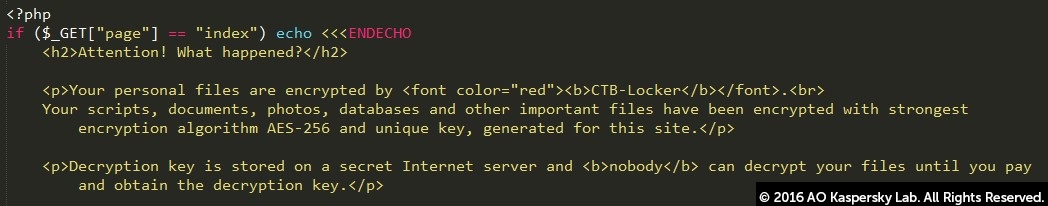
Ransomware encrypting web servers
- It targets webservers and encrypts a number of the files on it.
- Known vulnerabilities in the Content Management Systems are often used to deploy ransomware on web services.
Mobile device ransomware (Android)
- Mobile devices (mostly Android) can be infected via “drive-by downloads”.
- They can also get infected through fake apps that masquerade as popular services such as Adobe Flash or an anti-virus product.
Paying the ransom is never recommended, mainly because it does not guarantee a solution to the problem. There are also a number of issues that can go wrong accidentally. For example, there could be bugs in the malware that makes the encrypted data unrecoverable even with the right key.
In addition, if the ransom is paid, it proves to the cybercriminals that ransomware is effective. As a result, cybercriminals will continue their activity and look for new ways to exploit systems that result in more infections and more money on their accounts.
A ransomware attack is typically delivered via an e-mail attachment which could be an executable file, an archive or an image. Once the attachment is opened, the malware is released into the user’s system. Cybercriminals can also plant the malware on websites. When a user visits the site unknowingly, the malware is released into the system.
The infection is not immediately apparent to the user. The malware operates silently in the background until the system or data-locking mechanism is deployed. Then a dialogue box appears that tells the user the data has been locked and demands a ransom to unlock it again. By then it is too late to save the data through any security measures.
For more information please see the video below:
Any consumer and any business can be a victim of ransomware. Cybercriminals are not selective, and are often looking to hit as many users as possible in order to obtain the highest profit.
Yes, because cybercriminals know that organizations are more likely to pay as the data held captive is typically both sensitive and vital for business continuity. In addition, it can sometimes be more expensive to restore backups than to pay a ransom.
Ransomware is on the rise – there are now more than 50 families of this malware in circulation — and it’s evolving quickly. With each new variant comes better encryption and new features. This is not something you can ignore!
One of the reasons why it is so difficult to find a single solution is because encryption in itself is not malicious. It is actually a good development and many benign programs use it.
The first crypto-malware used a symmetric-key algorithm, with the same key for encryption and decryption. Corrupted information could usually be deciphered successfully with the assistance of security companies. Over time, cybercriminals began to implement asymmetric cryptography algorithms that use two separate keys — a public one to encrypt files, and a private one, which is needed for decryption.
The CryptoLocker Trojan is one of the most famous pieces of ransomware. It also uses a public-key algorithm. As each computer is infected it connects to the command-and-control server to download the public key. The private key is accessible only to the criminals who wrote the CryptoLocker software. Usually, the victim has no more than 72 hours to pay the ransom before their private key is deleted forever, and it is impossible to decrypt any files without this key.
So you have to think about prevention first. Most antivirus software already includes a component that helps to identify a ransomware threat in the early stages of infection, without occurring the loss of any sensitive data. It is important for users to ensure that this functionality is switched on in their antivirus solution.
The “No More Ransom” project has just started, but we are continuously working with other security companies and law enforcement agencies to identify as many keys as possible, for as many variants as possible. If you have some information that you think can help, please share it with us.
The Crypto Sheriff is a tool that is designed to help us define the type of ransomware affecting your device. This will enable us to check whether there is a decryption solution available. Please see the video below to see how it works:
This is possible. Sometimes we only get a subset of the keys, so please keep checking the website.
It is possible in the following cases:
- The malware authors made an implementation mistake, making it possible to break the encryption. That was the case with the Petya ransomware and with the CryptXXX ransomware.
- The malware authors feel sorry about their actions and publish the keys, or a "master key", as in the TeslaCrypt case.
- Law enforcement agencies seize a server with keys on it and share them. One such example is CoinVault.
Sometimes paying the ransom also works, but there is no guarantee that paying will actually lead to your files being decrypted. In addition, you 're supporting the criminal's business model and thus are partly responsible for more and more people getting infected with ransomware.
It's no secret that ransomware, which encrypts data on users' systems and then demands a ransom, has become a huge problem for cybersecurity over the last few years. It has become so widespread that it could easily be called an epidemic. The number of users attacked with ransomware is soaring, with 718.000 users hit between April 2015 and March 2016: an increase of 5.5 times compared to the same period in 2014-2015.
The police cannot fight cybercrime, and ransomware in particular, on its own. And security researchers cannot do it without support from law enforcement agencies. Responsibility for the fight against ransomware is shared between the police, the justice department, Europol and IT security companies, and requires a joint effort. Together we will do everything in our power to disrupt criminals' money-making schemes and return files to their rightful owners, without the latter having to pay loads of money.
"No More Ransom" is an international initiative that shows the value of public-private cooperation when taking serious action cybercrime. This collaboration goes beyond geographical borders. The main aim of the project is to share knowledge and educate users across the world on how to prevent ransomware attacks. We believe that it will eventually lead to support for repairing the damage caused to victims all around the globe. By restoring access to their systems, we empower users by showing them they can take action and avoid rewarding criminals with a ransom payment.
In its initial stage, the portal contains a four decryption tools for different types of malware. All tools available on the website are free, and they will work for any user infected with the threat mentioned at the website - regardless of where they are located in the world.